
A cyberespionage menace actor tracked as Billbug (a.k.a. Thrip, Lotus Blossom, Spring Dragon) has been jogging a campaign concentrating on a certification authority, governing administration businesses, and protection organizations in various nations around the world in Asia.
The most latest assaults had been noticed given that at minimum March but the actor has been running stealthily for extra than a ten years and it is thought to be a condition-sponsored group working for China.
Its operations have been documented by numerous cybersecurity businesses above the past 6 years [1, 2, 3].
Security researchers at Symantec say in a report today that Billbug, who they have been tracking due to the fact 2018, also qualified a certificate authority organization, which would have permitted them to deploy signed malware to make it a lot more challenging to detect or to decrypt HTTPS site visitors.
New campaign, aged resources
Symantec has not decided how Billbug gains preliminary accessibility to the goal networks but they have witnessed proof of this happening by exploiting public-experiencing apps with recognised vulnerabilities.
Like in previous strategies attributed to Billbug, the actor brings together tools that are already current on the focus on technique, publicly out there utilities, and personalized malware. Among the them are:
- AdFind
- Winmail
- WinRAR
- Ping
- Tracert
- Route
- NBTscan
- Certutil
- Port Scanner
These resources enable hackers mix with innocuous each day action, stay clear of suspicious log traces or raising alarms on safety applications, and frequently make attribution attempts more challenging.
A extra seldom deployed open up-supply device observed in recent Billbug operations is Stowaway, a Go-primarily based multi-level proxy tool that allows pentesters bypass network access restrictions.
Symantec was ready to pin the modern assaults to Billbug mainly because the threat actor applied two personalized backdoors seen in some of their previous operations: Hannotog and Sagerunex.
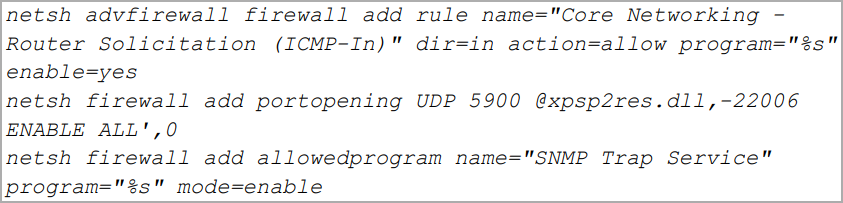
Some functionalities of the Hannotog backdoor consist of changing firewall configurations to empower all site visitors, build persistence on the compromised machine, add encrypted info, operate CMD commands, and download documents to the machine.
Sagerunex is dropped by Hannotog and injects alone in an “explorer.exe” course of action. It then writes logs on a area temp file encrypted utilizing the AES algorithm (256-bit).
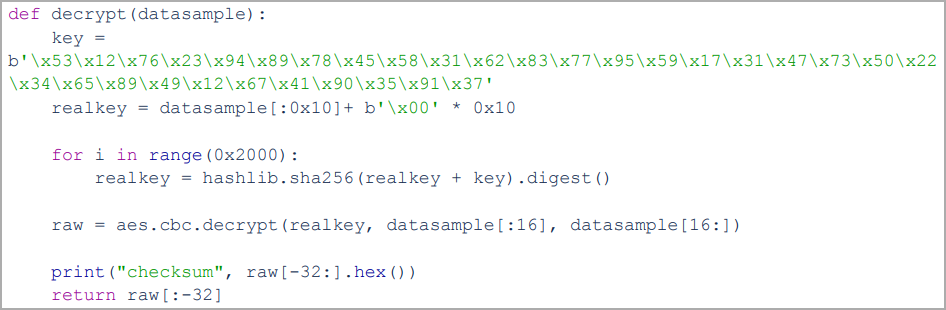
The backdoor’s configuration and point out are also saved regionally and encrypted with RC4, with the keys for both equally being hardcoded into the malware.
Sagerunex connects to the command and command server via HTTPS to mail a checklist of energetic proxies and documents, and receives payloads and shell instructions from the operators. In addition, it can execute programs and DLLs making use of “runexe” and “rundll.”
Billbug carries on to use the exact custom backdoors with negligible changes over the past years.





More Stories
Arranging To Obtain A New MIDI Keyboard Controller?
Substantial Flying Inventory: L Intercontinental Pcs, Inc. The Following DELL?
What is Ecc Memory?